EY refers to the global organization, and may refer to one or more, of the member firms of Ernst & Young Limited, each of which is a separate legal entity. Ernst & Young Limited is a Swiss company with registered seats in Switzerland providing services to clients in Switzerland.
How EY can help
-
Discover how EY's identify and access management (IAM) team can help your organization manage digital identities for people, systems, services and users.
Read more -
EY Crisis Management & Incident Response enables business leaders to recognize, prepare for, respond to and recover from crisis threats. Learn more.
Read more
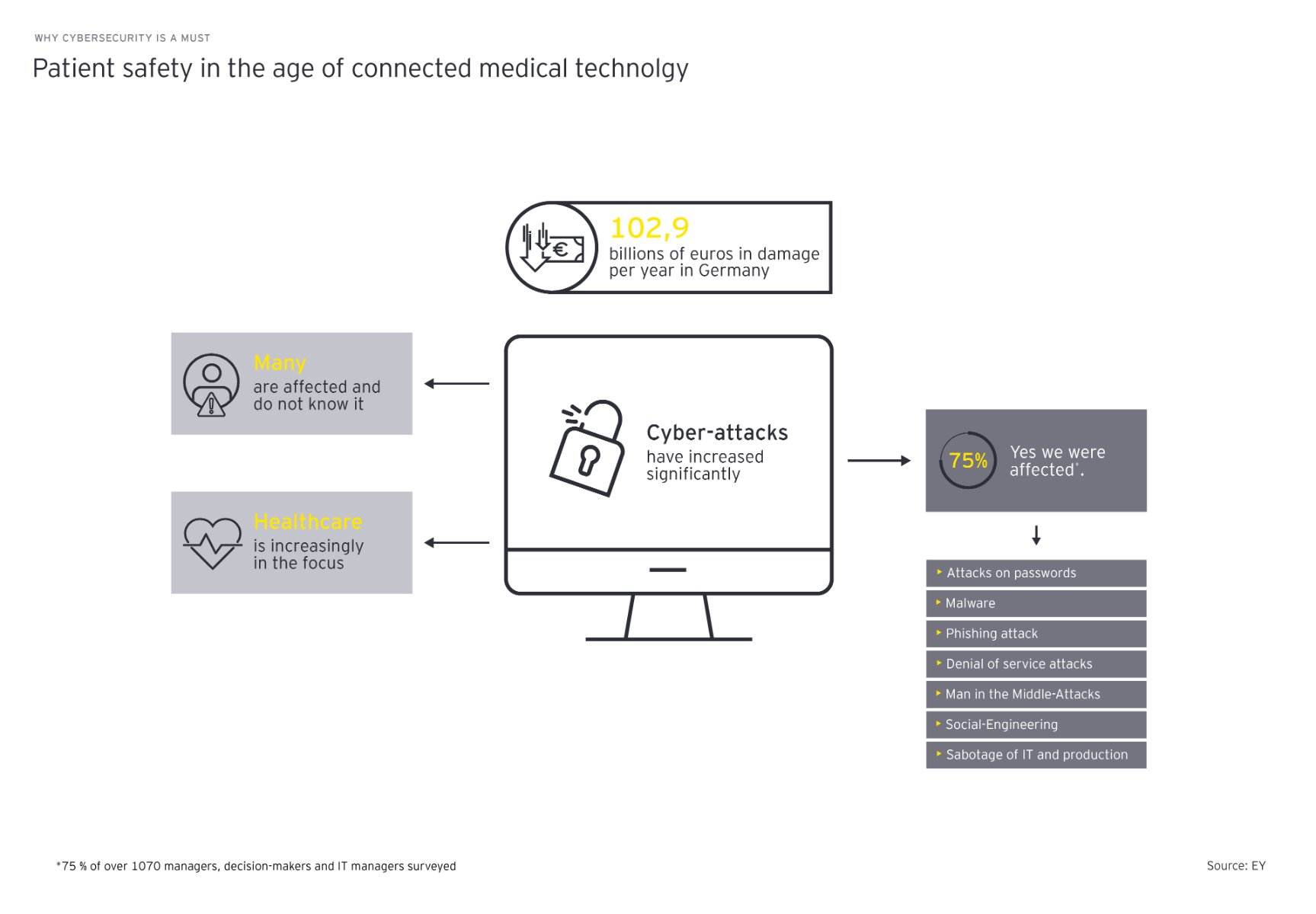
Hospitals, doctors’ surgeries, emergency services, laboratories, drug authorities, pharmaceutical companies, universities or manufacturers of medical devices – a cyber attack can affect any organization, as recent incidents show. The motives of the criminals are as varied as their methods. Extortion of ransom, identity theft, activists who want to make their concerns heard, but also cyber espionage and targeted – often state-sponsored – attacks on critical infrastructures (KRITIS) to unsettle the population play a role.
A hacker attack can not only have health consequences for patients, but also means the loss of sensitive data. This is not insignificant, because the health-related data is very personal and misuse could even allow identity theft. In addition, a cyber attack often involves considerable reputational damage and the loss of a lot of money for the companies concerned. If IT or production fails for a longer period of time, or if operationally necessary data and systems cannot be restored quickly, this can threaten the company’s existence. Moreover, anyone who pays the demanded ransom in the hope of quickly regaining access to the data may be liable to prosecution.
Raising protective shields: How medical device companies can prepare for cyber attacks
Even if the methods of cybercriminals are becoming more and more perfidious, surrender to cyber threats is not a solution. Suppliers of medical devices, in particular, have a responsibility in this respect, which, in fact, is also required by law. Cyber risks and vulnerabilities that may affect internal IT, production or manufactured products must be continuously analyzed and remedied. This is uncomfortable, but compared to a hacker attack that paralyzes production or entire facilities, it is still the lesser evil. In order to keep up with the methods of the attackers, however, a look at the technology alone does not go far enough. In addition to the products, the processes and regulatory requirements must also be considered. Along with a crisis plan, which should be regularly practiced in simulations, preparation therefore also includes building a powerful cybersecurity team with the necessary qualifications and competencies.